-
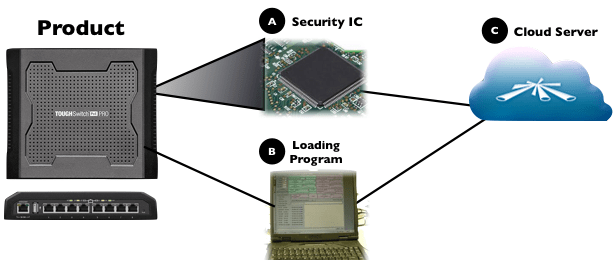
Manufacturing in China and IP Protection
Over the past decade, electronics manufacturing has largely shifted into China because of cost-savings. However, these cost-savings can often be misleading as manufacturing in China also comes with the risk of IP theft that can potentially lead to financial damages far in excess of the capital saved in manufacturing there. As a hi-volume hardware manufacturing…
-
Disrupting Markets: The Walmart Story
Last weekend I had the pleasure of having dinner with Pitt Hyde, the Founder of AutoZone (NYSE:AZO) and just an overall impressive, humble, and great person. Perhaps my favorite story of his was when he recounted his time serving on Sam Walton’s Walmart Board of Directors in the early days of his company. According to…
-
What is the Future of TV?
I want to preface this post by saying I have very little knowledge about the business side of television. The below analysis is the result of some surface investigation combined with my own experience in building new technology platforms, attacking distribution inefficiencies, and disrupting markets. This weekend, I decided to finally take a look at…
-
Beijing
This week I was in Beijing working on a PR campaign to build awareness of the Ubiquiti Networks brand in China. Beijing’s development pace has been astounding and the quality standards of their airport, shopping districts, hotels, and business centers now rival those of Dubai or even Tokyo. The city is very alive and I…
-
Walk the Walk
Unfortunately in the world we live in, there are the few that truly create value and then there are the many that prey off the value creation of these few. One of my favorite movie scenes — from the classic “Hustle and Flow,” about a struggling Memphian (Djay) who enlists the help of a music…
-
BootStrapping Strategies Part 5: The Power of Information Transparency
One of my favorite movie scenes is from the comedy Office Space about the miserable culture of Initech, a software development company. When the company brings in two so-called “efficiency experts” to restructure its operations, the experts start by interviewing each employee to determine who essentially needs to be replaced. One of their interviews focuses…
-
A Look into Ubiquiti’s R&D Strategy: Introducing mFI
Background: In 2001, the IEEE published the initial 802.16d Wimax fixed broadband wireless technology standard hoping it would bridge the digital divide amongst the underserved world. Intel heavily backed Wimax and envisioned an interoperable technology standard supported by a consortium of chipset and system manufacturing companies that would eventually drive hardware price points down to…
-
BootStrapping Strategies Part 4: Building Defensibility
When Ubiquiti released the NanoStation “customer premise equipment” (CPE) in 2008, it changed the “Wireless Internet Service Provider” (WISP) market. WISP’s (much like Ubiquiti) typically started as bootstrapped entrepreneurial ventures that were cash flow constrained. With the introduction of the disruptive cost/performance NanoStation CPE, Ubiquiti provided a near zero time return on capital investment to…
-
BootStrapping Strategies Part 3: Product Development Models: Predictive vs. Reactive
In Part 2, I talked about Ubiquiti Networks’ beginnings that started with a flawed business strategy and eventually evolved to define a market. Before I tell the follow-on story, I would like to preface it with a discussion of how I see two kinds of product development models: “predictive” and “reactive.” A predictive development model…
-
Commoditization and Leverage
When a technology product is brought to market, it is typically the result of several partners working together. For instance, an Android phone is the result of companies like HTC or Samsung productizing Google’s underlying mobile operating system platform and partnering with mobile carriers such as AT&T and Verizon who use their networks and stores…

You must be logged in to post a comment.